Beeper
Beeper Mini, the Android app born from a reverse-engineering of Apple’s iMessage service, is currently broken, and it is unknown whether it will resume functioning.
Beeper desktop users received a message from co-founder Eric Migicovsky late on Friday afternoon, noting an “iMessage outage” and that “messages are failing to send and receive.” Reports had started piling up on Reddit around 2:30 pm Eastern. As of 5:30 pm, the app was still reporting errors in sending and receiving messages, with “Failed to lookup on sever: lookup request timed out.” Comments on Beeper’s status post on X (formerly Twitter) suggested mixed results, at best, among users.
The Verge, messaging with Migicovsky, reported that he “did not deny that Apple has successfully blocked Beeper Mini”; to TechCrunch, Migicovsky more clearly stated about an Apple cut-off: “Yes, all data indicates that.” To both outlets, Migicovsky offered the same comment, re-iterating his belief that it was in the best interests of Apple to let iPhone owners and Android users send encrypted messages to one another. (Ars reached out to Migicovsky for comment and will update this post with new information).
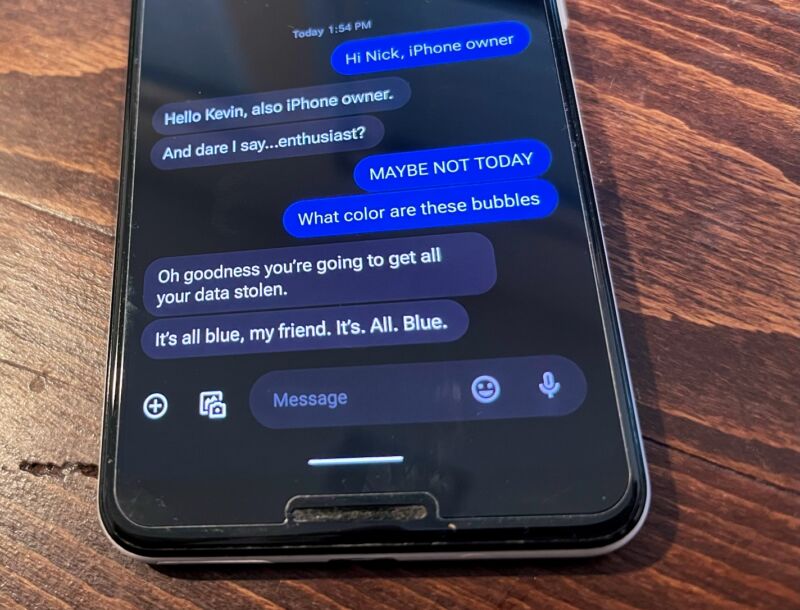
Beeper, as it worked shortly before launch on Dec. 5, sending iMessages from a Google Pixel 3 Android phone.
Kevin Purdy
Beeper’s ability to send encrypted iMessages from Android phones grew from a teenager’s reverse-engineering of the iMessage protocol, as Ars detailed at launch. The app could not read message contents (nor could Apple), kept encryption keys and contacts on your device, and did not require an Apple ID to authenticate.
The app did, however, send a text message from a device to an Apple server, and the response was used to generate an encryption key pair, one for Apple and one for your device. A Beeper service kept itself connected to Apple’s servers to notify it and you about new messages. Reddit user moptop and others suggested that Beeper’s service used encryption algorithms whose keys were spoofed to look like they came from a Mac Mini running OS X Mountain Lion, perhaps providing Apple a means of pinpointing and block them.
Members of the Discord focused on the original reverse-engineered tool on which Beeper Mini was built, PyPush, also reported that the tool was down Friday evening. Some noted that it seemed like their phone numbers had additionally been de-registered from iMessage.
Beeper Mini’s iMessage capabilities, for which the company was planning to charge $1.99 per month after a seven-day trial, were more than a feature. The company had planned to build additional secure messaging into Beeper Mini, including Signal and WhatsApp messaging, and make it the primary focus of its efforts. Its prior app Beeper, temporarily renamed Beeper Cloud, was marked to be deprecated at some point in favor of the new iMessage-touting Mini app.